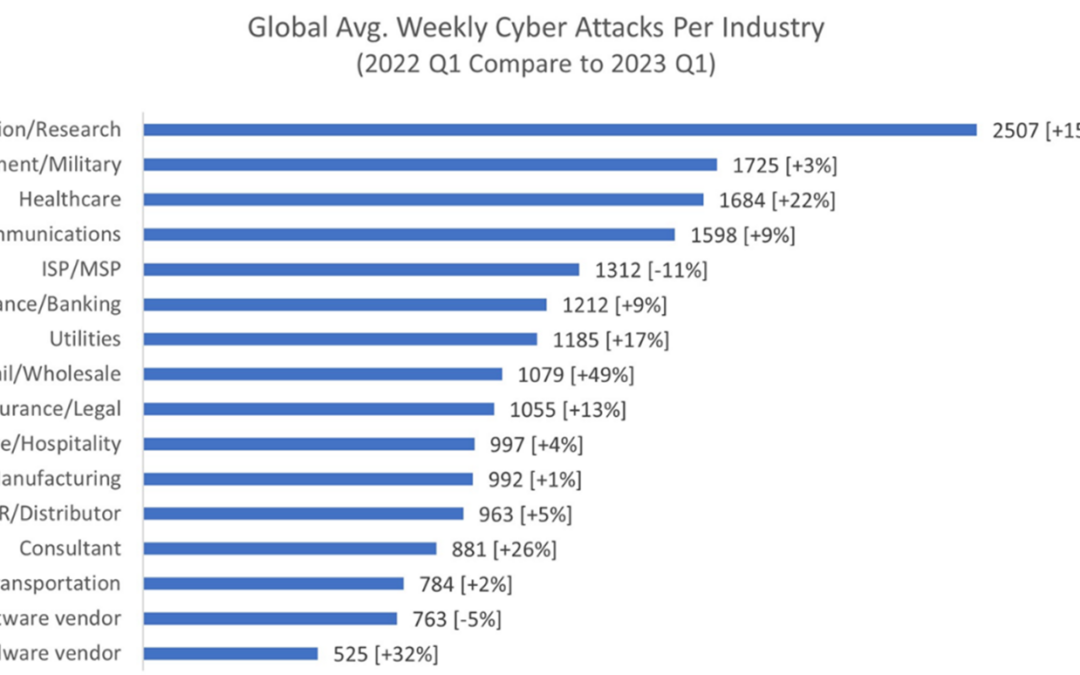
The global prevalence of cyber-crime in healthcare has increased exponentially in recent years. According to the World Economic Forum, since 2016, the number of confirmed cyber attacks against healthcare organizations has doubled, and strikingly between 2022-2023, the rate of increase has reached 22%.
A lot can of course be said about how threats evolve, and how cyber criminals are utilizing increasingly sophisticated techniques that are becoming ever more challenging to tackle. Yet whatever the speed of development in cyber-crime, as part of our collective effort to maximize the protection of healthcare data, there is a simple concept that should be brought to the forefront.
Worldwide, cyber criminals exploit the vulnerabilities of healthcare organizations. However, the fewer systems that are in place, the fewer systems there are to be attacked. In a nutshell, retiring old applications also minimizes the likelihood of becoming a victim of an attack – an incident which can prove not only incredibly costly, but can also damage reputation and trust.
The term ‘legacy’ unravelled
In fact, experience shows that most mature healthcare facilities have one legacy application or data repository per bed; a colossal number. Imagine a facility with 400 beds, that is a lot of additional points of entry for cyber criminals to exploit.
‘Legacy,’ ‘legacy application’, and ‘legacy data repository’ are terms frequently used across the healthcare industry, but what do they really mean? Quite simply, a legacy application is one that no longer generates new content. It may, and likely does, contain data that’s still referenced and considered important and, to this end, could be called a ‘reference application’. Of course, another point that should be considered is whether the application is being accessed, even if it isn’t generating new data.
Content may not be accessed for one of two reasons: firstly, if the data isn’t valid or important anymore; and, secondly, if consumers of the data can’t access the application or data repository.
When considering cyber-crime mitigation, if the data truly is of no value anymore, then it should be removed. In the world of Machine Learning and AI, it’s not always possible to determine if a dataset becomes valuable in the future. It could be argued that’s why many applications are retained, simply because the concept of ‘big data’ means that most data has some intrinsic value.
This moves us onto another question of why legacy applications are likely to be more vulnerable to attack. Most legacy applications are likely to be based on unsupported hardware and operating systems – an issue recently addressed by the UK Prime Minister who stated that the NHS could have as many as 12,000 systems still running windows 7 (an operating system first introduced in 2009, which hasn’t had any updates since 2020 when Microsoft ended support). However, often it’s not the application itself that’s vulnerable, it’s the middleware on which it sits that poses the biggest risk.
Tools to boost cyber resilience
BridgeHead has a process for migrating content from almost any application and moving it to a single, central Clinical Data Repository (CDR). Our team provides tools that can be considered ETL (Extract Transform and Load), where the data is extracted from the existing legacy application using a variety of methods. It is then transformed into a standard, enabling all data to be viewable from a single repository, regardless of its origin. Demographics and multiple patient numbering schemes are managed allowing data to be linked to a common patient. Next the data is ‘loaded’ into BridgeHead’s CDR, HealthStore®.
Once the data is successfully migrated, the original application is decommissioned, which usually means there is one final backup before being ‘switched off’. Critically, this cyber-attack entry point is removed, and the threat surfaced reduced.
Returning to the situation in which data isn’t accessed because it is ‘too hard’ to find in the original system. Through using BridgeHead’s Clinical Portal (part of HealthStore), data is easy to access. Additionally, training is required on only one system to allow easy access to all legacy data and, what’s more, this data can even be embedded in current and future EHRs.
Why won’t the Clinical Data Repository be attacked?
Legacy data migration facilitates better control over data assets and a CDR reduces the risk of cyber-attack. Firstly, this is thanks to fewer entry points and fewer historic operating systems in situ, and on the grounds that the CDR is kept up-to-date with patching to further reduce vulnerabilities. Importantly the CDR is also resilient to attack as it ensures data is always hidden behind firewalls (APIs), consequently cyber bots cannot crawl that data.
Secondly, the CDR is resilient to attack by ensuring that there are multiple copies of data, held in multiple locations. Furthermore, BridgeHead does not use replication, which means if one copy of data becomes compromised by malware, other copies won’t be overwritten.
Also, cyber-crime is breathing life back into the concept of offline data (e.g. tape) because if data is offline, it can’t be accessed by malware bots. Instead, its catalogued and ready to be recalled as a ‘last resort’.
Fewer, means more secure
Fundamentally, reducing the number of systems also lowers the likelihood of cyber-attack simply because it decreases the threat surface. Whilst the risk of cyber-attack can never be eliminated, there are steps that can be taken to minimize the risk whilst also dramatically improving access to legacy data. This is a real win-win.
Jamie Clifton is the Head of Innovation and Research for BridgeHead Software.
Jamie has been involved with Enterprise Data management for 12 years for many of the world’s foremost software companies. He currently drives the product strategy for BridgeHead’s archiving product line into the healthcare sector focusing specifically on Vendor Neutral Archiving (VNA) and Cross Enterprise Document Sharing (XDS). Jamie holds BSc (Hons) degree in Computing Science and Economics.
To learn how BridgeHead can help you reduce your cybersecurity risks and save cost by retiring your legacy applications…